After a long hiatus of over 5 months (in which time I started working for an awesome company called AdMob), I thought of restarting the blog after reading an interesting article about decrypting voice signals over the air. If channel hopping were the whole source of trust in GSM voice security, it was just a matter of time before the same was broken. Now, it will be interesting to see how more security features are added and if they will stand the test.
"If the GSM Association's excuse for bad crypto is there is another security feature we rely on much more, then of course, we'll break that, too." :)
Monday, December 28, 2009
Friday, July 10, 2009
Thursday, July 2, 2009
Long time..
Well, been caught up in the paypal project and boy! is it interesting :)
On a completely different topic, came across a piece of interesting trivia while reading about the page rank algorithm in wikipedia- Apparently Stanford got 1.8mil shares from Google so that they could use Larry Page's algorithm (the patent for which was, of course, granted to Stanford) and sold it for $336mil in 2005. And I thought the 250 bucks I spend on each hour class at Carnegie Mellon was ridiculous!
On a completely different topic, came across a piece of interesting trivia while reading about the page rank algorithm in wikipedia- Apparently Stanford got 1.8mil shares from Google so that they could use Larry Page's algorithm (the patent for which was, of course, granted to Stanford) and sold it for $336mil in 2005. And I thought the 250 bucks I spend on each hour class at Carnegie Mellon was ridiculous!
Wednesday, June 3, 2009
Bug in Google Calendar
I was trying to share my calendar with myself to test the privacy features of the calendar and I added an invite from one of my google accounts to another for the same. After I clicked on the link that appeared in my invitee account's mail, here's what I got.

And the url is https://www.google.com/a/sv.cmu.edu/ServiceLogin?service=cl&passive=true&nui=1&continue=http%3A%2F%2Fwww.google.com%2Fcalendar%2Fhosted%2Fsv.cmu.edu%2Frender%3Fshare%3Dnehagp2%2540gmail.com
And the url is https://www.google.com/a/sv.cmu.edu/ServiceLogin?service=cl&passive=true&nui=1&continue=http%3A%2F%2Fwww.google.com%2Fcalendar%2Fhosted%2Fsv.cmu.edu%2Frender%3Fshare%3Dnehagp2%2540gmail.com
Thursday, May 7, 2009
Robust programming
I was recently checking out what dead beef signifies and came across a blog with the name Dead Beef Cafe, which was apparently started by a few friends to talk about computer security, food and geeky stuff. An interesting read from one of the posts was Matt Bishop's writeup on Robust programming. It is quite amazing how most of the code that you would write in the first shot is most likely to be fragile. One of the conclusions I drew after reading the article was that working on Java was so much better than writing code in C! It takes care of so many of the factors mentioned in the article. Well, more on that later..
And of course, dead beef is actually a hexadecimal code 0xdeadbeef which was used by IBM in its RS/6000 series to signify freshly allocated memory. Some modern debugging tools deliberately fill freed memory with this value as a way of converting heisenbugs into Bohr bugs. As in “Your program is DEADBEEF” (meaning gone, aborted, flushed from memory) Some of the other amusing hexcodes that are/were used:
DEADDEAD - A Microsoft Windows STOP Error code used when the user manually initiates the crash.
ABADBABE - Used by Apple as the "Boot Zero Block" magic number (dunno what boot zero block is but that's funny)
C0DEDBAD - A memory leak tracking tool which it will change the MMU tables so that all references to address zero
And of course, dead beef is actually a hexadecimal code 0xdeadbeef which was used by IBM in its RS/6000 series to signify freshly allocated memory. Some modern debugging tools deliberately fill freed memory with this value as a way of converting heisenbugs into Bohr bugs. As in “Your program is DEADBEEF” (meaning gone, aborted, flushed from memory) Some of the other amusing hexcodes that are/were used:
DEADDEAD - A Microsoft Windows STOP Error code used when the user manually initiates the crash.
ABADBABE - Used by Apple as the "Boot Zero Block" magic number (dunno what boot zero block is but that's funny)
C0DEDBAD - A memory leak tracking tool which it will change the MMU tables so that all references to address zero
Sunday, May 3, 2009
GLAT
The GLAT (that's the Google Labs Aptitude Test) was announced in 2004 in a magazine like an advertise for people who might be intrigued by the test and the questions they saw in it. The test was interesting, one of the more interesting questions though was
Consider a function which, for a given whole number n, returns the number of 1s required when writing out all numbers between 0 and n. For example f(13)=6. What is the next largest n such that f(n)=n?
One of the more obvious solutions:
public static int f(int n) {
int f = 1;
for (int i=2;i<=n;i++) {
int j = 10;
int i1 = i;
while (i1/j > 0) {
if ((int)(i1/j) == 1)
f++;
if ((int) (i1%j) == 1)
f++;
i1 = i1/10;
}
}
return f;
}
Returned the correct answer: 199981
The solution is obviously pretty bad, but I guess I'm gonna improve it only after a good night's sleep :P
Consider a function which, for a given whole number n, returns the number of 1s required when writing out all numbers between 0 and n. For example f(13)=6. What is the next largest n such that f(n)=n?
One of the more obvious solutions:
public static int f(int n) {
int f = 1;
for (int i=2;i<=n;i++) {
int j = 10;
int i1 = i;
while (i1/j > 0) {
if ((int)(i1/j) == 1)
f++;
if ((int) (i1%j) == 1)
f++;
i1 = i1/10;
}
}
return f;
}
Returned the correct answer: 199981
The solution is obviously pretty bad, but I guess I'm gonna improve it only after a good night's sleep :P
Thursday, April 30, 2009
Architectural principles of the internet from way back in 1996
I was reading the RFC 1958 to understand the architectural principles laid down for the internet way back in 1996 and came across an interesting term the 'end to end argument', which is discussed in depth in a paper by Saltzer et al .
The basic argument is that, as a first principle, certain required end-
to-end functions can only be performed correctly by the end-systems
themselves. A specific case is that any network, however carefully
designed, will be subject to failures of transmission at some
statistically determined rate. The best way to cope with this is to
accept it, and give responsibility for the integrity of communication
to the end systems. Another specific case is end-to-end security.
To quote from [Saltzer], "The function in question can completely and
correctly be implemented only with the knowledge and help of the
application standing at the endpoints of the communication system.
Therefore, providing that questioned function as a feature of the
communication system itself is not possible. (Sometimes an incomplete version of the function provided by the communication system may be useful as a performance enhancement.")
Though this is applicable mostly to reliability and availability, an interesting thing is that it doesn't quite equally apply verbatim to security. The dynamics of the internet and security requirements have changed to such an extent (as also noted by Bradner here), that this argument (which the architecture of the internet is based on) does not seem to be as applicable to security any more.
[PS: I cannot believe that there are no updates since RFC 1958]
The basic argument is that, as a first principle, certain required end-
to-end functions can only be performed correctly by the end-systems
themselves. A specific case is that any network, however carefully
designed, will be subject to failures of transmission at some
statistically determined rate. The best way to cope with this is to
accept it, and give responsibility for the integrity of communication
to the end systems. Another specific case is end-to-end security.
To quote from [Saltzer], "The function in question can completely and
correctly be implemented only with the knowledge and help of the
application standing at the endpoints of the communication system.
Therefore, providing that questioned function as a feature of the
communication system itself is not possible. (Sometimes an incomplete version of the function provided by the communication system may be useful as a performance enhancement.")
Though this is applicable mostly to reliability and availability, an interesting thing is that it doesn't quite equally apply verbatim to security. The dynamics of the internet and security requirements have changed to such an extent (as also noted by Bradner here), that this argument (which the architecture of the internet is based on) does not seem to be as applicable to security any more.
[PS: I cannot believe that there are no updates since RFC 1958]
Tuesday, April 28, 2009
Unleashing the power of Google
In a book by Chris Sherman, named Google Power.. , he writes of an article that he authored way back in June 1999. At the time Google was still on its way to becoming popular and was laying its foundations. Something striking from the interview in the article:
'Unlike the major search engines, Google is a "pure" search engine. No news, email, chat, stock quotes or other trappings offered by major portals. And Page says that Google intends to keep it that way, focusing the companies energies strictly on search.'
:)
'Unlike the major search engines, Google is a "pure" search engine. No news, email, chat, stock quotes or other trappings offered by major portals. And Page says that Google intends to keep it that way, focusing the companies energies strictly on search.'
:)
Sunday, April 26, 2009
Rootkits
Some information I got from Neil Daswani's book Foundations of Security : A rootkit is a set of impostor operating system tools (tools that list the set of active processes, allow users to change passwords, etc.) that are meant to replace the standard version of those tools such that the activities of an attacker that has compromised the system can be hidden. Once a rootkit is successfully installed, the impostor version of the operating system tools becomes the default version. A system administrator may inadvertently use the impostor version of the tools and may be unable to see processes that the attacker is running, files or log entries that result from the attacker’s activity, and even network connections to other machines created by the attacker.
Friday, April 24, 2009
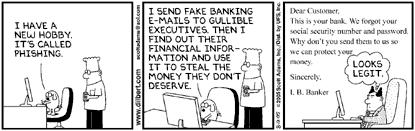
Context Aware Phishing
The security and privacy of context aware applications is important for several reasons, the most important one being that these applications have access to a lot of the user's personal information (like location, preferences, behavioral history, etc). What is more interesting is that phishing attacks can be taken one step further by using contextual information . As Markus et al talk in this paper, an attack considering context of a user would make him more gullible to the attack and less aware of any trust factors he should be looking for. Phishing, done through web sites, already does consider context in many cases. But when we talk about context aware mobile applications, what kind of attacks would be possible? If an attacker knows the locations you have recently visited, he could easily use that information into gaining your trust.
Tuesday, April 21, 2009
Anind Dey's talk
Yesterday, we had a presentation by and lunch with Anind Dey, an asst professor at Pittsburgh. He's currently working on applying human computer interaction to ubiquitous systems and context aware applications in particular. Among the projects he's working on, he explained a few which sounded very interesting. One of them involves the study of traffic and driving conditions on drivers, and using this information to improve intelligibility of navigation systems. For that project, he presented a paper at CHI-09 of a design to show the navigation on the windshield of a car, instead of having the driver distracted by a gps-like system. Another project involved a memory-logging system meant for alzheimer's disease patients. It consists of a camera that takes pictures every so seconds and helps these patients remember what they did in the recent past. He mentioned that one Prof Laura at Pittsburgh is also working on studying the usability of security and privacy in context aware mobile applications. Apparently, her findings show that the padlock is the least useful cue in conveying security in underlying transport. One of Anind's suggestions was that of using a change in the background color of the application in case of a connection to an insecure access point. Hmm.. need to get in touch with her soon!
Saturday, April 18, 2009
Idea
Over the past 3 months, I have been focusing on understanding how user's are affected by security and privacy cues in software applications (or other systems, like a car or house lock). One interesting idea that came to mind while reading the Clickbot.A paper was that we have not talked about the human factors (though indeed of a different nature) that influence security guarding agents, like anti virus companies or banks. What motivates them while dealing with security and fraud? An example that came up from the paper was that of anti virus companies spending time and money to identify a piece of software as being malicious, but they have no incentive for analyzing the behavior of bots that spread these malicious software. How do these factors affect software developers like us, and more so the public at large who use these software?
Friday, April 17, 2009
Neil Daswani's talk
Today we had a guest lecture by an ex-Google security expert, Neil Daswani. He was here to talk about web application attacks and current threats to information security. In less than an hour, I was introduced to several new terms, like Same Origin Policy , Google's Map Reduce , Drive-by-download , Clickbot.A and Malvertising . It'll take a week for me to get into the depths of each of these topics and write more about them, which is another reason why I'm glad I attended this lecture. The main reason, though, is that he told us more about the Advanced Computer Security Certificate at Stanford. The pricing sounds reasonable and the courses, very interesting. I definitely plan to go out there some time soon, after I get a job.
Wednesday, April 15, 2009
RSA Conference '09
The theme for the RSA conference this year is Edgar Allan Poe . The man set up a contest for people to submit to him a cipher and offered free subscription to Alexander Graham's magazine if anyone submitted a cipher which he could not break. The contest was closed six months later by Edgar, claiming that he had broken all the 100 ciphers sent to him as an entry to the contest. And all this, by the way, was in 1839!
Sunday, April 12, 2009
P2P Privacy
An interesting article from one of Schneier's blogs made me a more curious about privacy in peer to peer networks. This reminds me of the project idea that Keying was talking about in class - privacy and security perceptions of people using p2p networks. It would have been a good project to work on for sure.
Apparently, it is just as likely that the entity prying onto your system from a p2p network may be a legitimate company as it could be an attacker. How do you save yourself from such prying eyes? By installing open source tools like PeerGuardian or ProtoWall. I plan to do this some time soon. Will keep posting the results.
Apparently, it is just as likely that the entity prying onto your system from a p2p network may be a legitimate company as it could be an attacker. How do you save yourself from such prying eyes? By installing open source tools like PeerGuardian or ProtoWall. I plan to do this some time soon. Will keep posting the results.
Thursday, April 9, 2009
No more ADC?
The wait for ADC II has been long and quite annoying. Early this year I knew there was little hope in expecting an announcement anytime soon, or even this year. Specially since Google started handing out devices to their employees for free to get more people to build applications on their platform, instead of hosting another ADC. What came as a shock though, was that they removed all trace of ADC I from google.com entirely. How is that justified?! Boo-hoo Google!
Wednesday, April 8, 2009
Idea
An idea that came up during the guest lecture on Access Control today was to study the effectiveness of social controlling techniques in access control. An example of social control in access control is, say if you perform access control on a file by sending an email to all the people you want to grant access to and deny access to others by stating in the email "Do not share this file with anyone not in this mailing list".
Monday, April 6, 2009
Ultra-human vision
In continuation to the idea and implementation put forth by Pranav Mistry in 'Sixth Sense', this article at Next World takes it a step forward and talks about a research project undertaken by researchers at University of Washington, in which the use of contact lenses would replace the projection and the person wearing them could see all information that he needs about the object within his range. Would this work in conjunction with the transcranial magnetic simulator or would it need a different interface? So many interesting questions can be asked about a technology like this.
Saturday, April 4, 2009
Spim and more
An interesting article about the top 5 IM security risks features (surprisingly) at its 5th position a term called Spim . That is spam for instant messaging. So how does spim work? One source is from im server databases. People sell the account names alongwith any other demographic information to spammers and in turn these spammers will use bots to make life hell for you. So what happens when you reply to these bots? An interesting wiki article talks about a bot called The Great Hatsby which basically hooks two people who reply to the bot and pretends to be chatting with them both. An open source tool - bot sentry is apparently the most powerful anti-spim tool (as a plugin for Pidgin) which only allows messages to be sent to you from people in your friends list, your allow list or someone who gives a correct reply to a question you have already set for the tool to ask. Now, that's an intelligent yet really simple design.
Of course on a similar note, there are other techniques like splog, spasms (spaSMS. lol!), spamming on newsgroups and forums, etc.
Of course on a similar note, there are other techniques like splog, spasms (spaSMS. lol!), spamming on newsgroups and forums, etc.
Thursday, April 2, 2009
Integer Overflow
In my quest to check what other code attacks are possible because of vulnerabilities in the run time, I came across a method to perform integer overflow to indeed corrupt memory. The article clearly explains the opcodes too, which makes it so much easier to understand. Anyway, its getting late now and I'm not able to find a good integer overflow attack that can be actuated in Java, so I'm going to call it a night and hope I find more luck tomorrow :)
This one's for the viruses
When I googled for top ten all time worst viruses, I found an interesting article . Now what is interesting about this article is that most of the viruses listed are really old and the authors have been caught too. Nevertheless, a majority of these (and other new ones - the most popular one being Conficker ) exploit a single technique - buffer overflow. Besides other techniques, an interesting method used to exploit buffer overflows is NOP slide technique which uses the NOP (no operation) instruction to slide to the end of the buffer to get to the exact redirection of address to the start of the malicious shellcode. Though old, it definitely is interesting enough to make an entry into this blog.
Of course, more importantly, techniques to counter buffer overflow attacks. Apparently it is extremely important to use safe (bound checking) libraries and yet, how many times do we really do that?
Of course, more importantly, techniques to counter buffer overflow attacks. Apparently it is extremely important to use safe (bound checking) libraries and yet, how many times do we really do that?
Tuesday, March 31, 2009
Wikileaks
An interesting article about the inside story of child pornography led me to a website called Wikileaks.org. This website hosts articles from anonymous users about leakage of confidential government, corporate or religious information. The website, however, ensures that the source of the information will remain completely untraceable. It is interesting to note how ( here and here ) they do that. And after putting in so much effort how do they ensure that their contributors are, in fact, giving genuine content to the site? They claim here that they have never failed to wrongly determine that an article is authentic. Reminds me of why electronic voting systems cannot be widely deployed. Simply put, the authenticity of their claim seems as questionable as that of the documents they so confidently seem to promote.
In another amusing incident, a US district court judge ordered that wikileaks.org be removed from the DNS by its Californian host Dynadot. No doubt I saw only the IP address when I googled for wikileaks. Seems darn fishy to me!
In another amusing incident, a US district court judge ordered that wikileaks.org be removed from the DNS by its Californian host Dynadot. No doubt I saw only the IP address when I googled for wikileaks. Seems darn fishy to me!
Saturday, March 28, 2009
SMC and usability?
Our SNS class had a guest lecture on the topic of security in multi party computation today. Some of the concepts discussed are interesting because of the variety of complex problems they are aimed to solve and how they are implemented. One of the interesting applications of multi party computation could possibly be in wireless ad hoc networks and sensor networks. The speaker, while explaining where these protocols are important, mentioned that with multi party computation, you would essentially not require to place trust in any entity, since you could always disallow him from reading your sensitive information even by giving it to him and allowing him to perform certain other computations on it. Imagine when you would not need to trust ebay or bankofamerica simply because they are reputed. Not having to worry about trust whatsoever. A very interesting problem would then be how to design a system that uses such multi party computation. How useable would it be so that all entities involved understand all the implications of the underlying cryptographic protocol? If only these systems weren’t so computation intensive (though it shouldn’t be a problem with small number of entities like in ad hoc networks)
Friday, March 27, 2009
Terence Spies visits our SNS class
A few days back, we had a guest lecture by the CTO of Voltage Systems, Terence Spies (ironic name for a person working in security). Besides talking at length about key management and identity based encryption, he also mentioned that it is more likely that data would get compromised not in the few microseconds that is on the wire, but at the end points where it resides for a much longer time.
Tuesday, March 24, 2009
Idea
While doing our prototype for locationing, we were constantly referring to this paper for guidelines for designing the application for social location disclosure. It was a useful paper and in the process I realized that we were doing so much work in improving the design of context aware applications, we could as well write design guidelines for the same. For example, while reading the paper, we came across guidelines like: Allow Deception while sharing location. We came up with others like: Never share historic information while adding new friends, or always indicate when an "auto" feature is running in the background. I guess the list is still very crude right now, but I'm sure we're getting there :)
Monday, March 23, 2009
Idea
As part of this week's assignment, we need to do a literature survey and try to find out relevant research work done, for our human factors project- Study of security and privacy in context aware mobile applications. Since the context aware application we are using for our study is a social networking app with location and micro-blogging, it was obvious for me to start searching for related work done in usability of security and privacy in social applications. Surprisingly, there is no research done in this area (or so are my findings). I think this is an important area of work since there are several threats to your identity information because of social networks. More so, if social networks will be used in search , it is important to know how useable the security and privacy implemented in these networks is.
Google Bombs
Thursday, March 19, 2009
Applying design principles
In one of our last HSF class, we discussed about this paper and how feasible the design of systems that are both secure and usable really is. Though it seems to be counter-intuitive (mostly due to experience of badly designed software), Cynthia explained that it is indeed more natural to have a system that is inherently both – secure and usable. We talked about different systems in which the obvious thing to do was designed to be the safe thing to do. There were many examples of this, right from door knobs and cars to session logouts from web applications. This discussion got me into thinking about how context aware (and indeed any other) applications implement this design principle in mobile devices. If you look at how users are required to connect to the internet by choosing a network or by launching the browser, it just follows that a lot of work needs to be done in designing good applications which btw are also secure! I could write a whole paper analyzing which of Ka-Ping Yee’s design principles are applied in cell phone applications, and perhaps on how design could be improved by adhering to the principles. (Perhaps that would be a good ‘recommendation’ of our study)
Wednesday, March 18, 2009
Srizbi Botnet
An interesting Wikipedia article mentions that one particular botnet called Srizbi has been the number one cause of spam mail throughout the world. Apparently, this botnet suffered big damages when a hosting provider McColo was taken down, reducing global spam by 75%.
Tuesday, March 17, 2009
Social Engineering techniques
While reading an article about social engineering, I happened to find out more about the concept and a guide to avoiding such attacks in a Microsoft document here . It is interesting to read about how vulnerable people are nowadays to virtual attacks like IM attacks. With your information and your social network out in the open on the internet, it is so easy to spoof an IM account and use persuasive techniques to obtain information from you.
Another interesting concept that the guide talks about it Reverse Social Engineering, which is when the attacker waits for the victim to approach them and give them their information willfully. This happens generally when the attacker poses as a person in authority to whom the victim willfully hands out his sensitive information. I wonder how many social engineering (and especially reverse social engineering) attacks get reported within corporations.
Another interesting concept that the guide talks about it Reverse Social Engineering, which is when the attacker waits for the victim to approach them and give them their information willfully. This happens generally when the attacker poses as a person in authority to whom the victim willfully hands out his sensitive information. I wonder how many social engineering (and especially reverse social engineering) attacks get reported within corporations.
Friday, March 13, 2009
Technologies used in child pornography
Bruce Schneier's blog led me to this really interesting article about how the child pornography industry works. What is particularly interesting about the article is the technologies used to completely anonymize the servers holding the content. Including techniques like IPSec Tunneling and SSL Tunneling. In SSL tunneling, you setup an http proxy over ssh (like here) and then send all your data through the proxy so that your content server remains anonymous. So if you had a large bot of proxies and a handful of content servers, you could virtually keep these content servers safe forever.
So how are these sites advertised? Apparently through spamming. The revenue from the child porn business are divided into 40-60% for the payment processor and the bank (percentage rate will depend on how hard the material is), 20% of the operator and 20% of the marketers (in this case, spammers). The article goes on to mention that spammers use zombie computers to carry out their act, and infect these computers in turn. These infected computers could not only compromise the identity of the owner, but also serve as a content server through SOCKS proxying . Yet I have a lot of difficulty in digesting the claim "if you have an email address, there is a possibility that there is child pornography on your computer because you have received CP advertising. And if your computer is not 100% safe against Trojans, viruses and rootkits, there is the possibility that your computer is part of the vast child pornography network." I dont see how this would work with dynamic IPs. But then there are tools like DynDNS that take care of that?
If what the author says is to be believed, no doubt that so much effort goes into keeping an industry alive that would generate 200 mil site visits in a single month for a single website!
So how are these sites advertised? Apparently through spamming. The revenue from the child porn business are divided into 40-60% for the payment processor and the bank (percentage rate will depend on how hard the material is), 20% of the operator and 20% of the marketers (in this case, spammers). The article goes on to mention that spammers use zombie computers to carry out their act, and infect these computers in turn. These infected computers could not only compromise the identity of the owner, but also serve as a content server through SOCKS proxying . Yet I have a lot of difficulty in digesting the claim "if you have an email address, there is a possibility that there is child pornography on your computer because you have received CP advertising. And if your computer is not 100% safe against Trojans, viruses and rootkits, there is the possibility that your computer is part of the vast child pornography network." I dont see how this would work with dynamic IPs. But then there are tools like DynDNS that take care of that?
If what the author says is to be believed, no doubt that so much effort goes into keeping an industry alive that would generate 200 mil site visits in a single month for a single website!
Cryptic Treats
As part of our Human Factors in Security course, we were asked by our course instructor Cynthia, to start writing a journal, in which we put in our thoughts about security. It could include news articles, new ideas, thoughts on current trends, mental maps, anything that would put those grey cells to work. I haven't been able to find much time to do it though I really liked the idea a lot and enjoy the class every wednesday evening. It hadn't occurred to me till recently though, that i could write a blog instead of a really ugly word document! Hope this blog will have lots of content and be useful in the future :)
Subscribe to:
Comments (Atom)