An interesting article about the inside story of child pornography led me to a website called Wikileaks.org. This website hosts articles from anonymous users about leakage of confidential government, corporate or religious information. The website, however, ensures that the source of the information will remain completely untraceable. It is interesting to note how ( here and here ) they do that. And after putting in so much effort how do they ensure that their contributors are, in fact, giving genuine content to the site? They claim here that they have never failed to wrongly determine that an article is authentic. Reminds me of why electronic voting systems cannot be widely deployed. Simply put, the authenticity of their claim seems as questionable as that of the documents they so confidently seem to promote.
In another amusing incident, a US district court judge ordered that wikileaks.org be removed from the DNS by its Californian host Dynadot. No doubt I saw only the IP address when I googled for wikileaks. Seems darn fishy to me!
Tuesday, March 31, 2009
Saturday, March 28, 2009
SMC and usability?
Our SNS class had a guest lecture on the topic of security in multi party computation today. Some of the concepts discussed are interesting because of the variety of complex problems they are aimed to solve and how they are implemented. One of the interesting applications of multi party computation could possibly be in wireless ad hoc networks and sensor networks. The speaker, while explaining where these protocols are important, mentioned that with multi party computation, you would essentially not require to place trust in any entity, since you could always disallow him from reading your sensitive information even by giving it to him and allowing him to perform certain other computations on it. Imagine when you would not need to trust ebay or bankofamerica simply because they are reputed. Not having to worry about trust whatsoever. A very interesting problem would then be how to design a system that uses such multi party computation. How useable would it be so that all entities involved understand all the implications of the underlying cryptographic protocol? If only these systems weren’t so computation intensive (though it shouldn’t be a problem with small number of entities like in ad hoc networks)
Friday, March 27, 2009
Terence Spies visits our SNS class
A few days back, we had a guest lecture by the CTO of Voltage Systems, Terence Spies (ironic name for a person working in security). Besides talking at length about key management and identity based encryption, he also mentioned that it is more likely that data would get compromised not in the few microseconds that is on the wire, but at the end points where it resides for a much longer time.
Tuesday, March 24, 2009
Idea
While doing our prototype for locationing, we were constantly referring to this paper for guidelines for designing the application for social location disclosure. It was a useful paper and in the process I realized that we were doing so much work in improving the design of context aware applications, we could as well write design guidelines for the same. For example, while reading the paper, we came across guidelines like: Allow Deception while sharing location. We came up with others like: Never share historic information while adding new friends, or always indicate when an "auto" feature is running in the background. I guess the list is still very crude right now, but I'm sure we're getting there :)
Monday, March 23, 2009
Idea
As part of this week's assignment, we need to do a literature survey and try to find out relevant research work done, for our human factors project- Study of security and privacy in context aware mobile applications. Since the context aware application we are using for our study is a social networking app with location and micro-blogging, it was obvious for me to start searching for related work done in usability of security and privacy in social applications. Surprisingly, there is no research done in this area (or so are my findings). I think this is an important area of work since there are several threats to your identity information because of social networks. More so, if social networks will be used in search , it is important to know how useable the security and privacy implemented in these networks is.
Google Bombs
Thursday, March 19, 2009
Applying design principles
In one of our last HSF class, we discussed about this paper and how feasible the design of systems that are both secure and usable really is. Though it seems to be counter-intuitive (mostly due to experience of badly designed software), Cynthia explained that it is indeed more natural to have a system that is inherently both – secure and usable. We talked about different systems in which the obvious thing to do was designed to be the safe thing to do. There were many examples of this, right from door knobs and cars to session logouts from web applications. This discussion got me into thinking about how context aware (and indeed any other) applications implement this design principle in mobile devices. If you look at how users are required to connect to the internet by choosing a network or by launching the browser, it just follows that a lot of work needs to be done in designing good applications which btw are also secure! I could write a whole paper analyzing which of Ka-Ping Yee’s design principles are applied in cell phone applications, and perhaps on how design could be improved by adhering to the principles. (Perhaps that would be a good ‘recommendation’ of our study)
Wednesday, March 18, 2009
Srizbi Botnet
An interesting Wikipedia article mentions that one particular botnet called Srizbi has been the number one cause of spam mail throughout the world. Apparently, this botnet suffered big damages when a hosting provider McColo was taken down, reducing global spam by 75%.
Tuesday, March 17, 2009
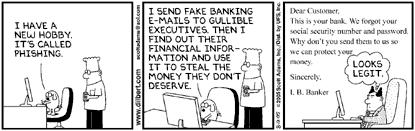
Social Engineering techniques
While reading an article about social engineering, I happened to find out more about the concept and a guide to avoiding such attacks in a Microsoft document here . It is interesting to read about how vulnerable people are nowadays to virtual attacks like IM attacks. With your information and your social network out in the open on the internet, it is so easy to spoof an IM account and use persuasive techniques to obtain information from you.
Another interesting concept that the guide talks about it Reverse Social Engineering, which is when the attacker waits for the victim to approach them and give them their information willfully. This happens generally when the attacker poses as a person in authority to whom the victim willfully hands out his sensitive information. I wonder how many social engineering (and especially reverse social engineering) attacks get reported within corporations.
Another interesting concept that the guide talks about it Reverse Social Engineering, which is when the attacker waits for the victim to approach them and give them their information willfully. This happens generally when the attacker poses as a person in authority to whom the victim willfully hands out his sensitive information. I wonder how many social engineering (and especially reverse social engineering) attacks get reported within corporations.
Friday, March 13, 2009
Technologies used in child pornography
Bruce Schneier's blog led me to this really interesting article about how the child pornography industry works. What is particularly interesting about the article is the technologies used to completely anonymize the servers holding the content. Including techniques like IPSec Tunneling and SSL Tunneling. In SSL tunneling, you setup an http proxy over ssh (like here) and then send all your data through the proxy so that your content server remains anonymous. So if you had a large bot of proxies and a handful of content servers, you could virtually keep these content servers safe forever.
So how are these sites advertised? Apparently through spamming. The revenue from the child porn business are divided into 40-60% for the payment processor and the bank (percentage rate will depend on how hard the material is), 20% of the operator and 20% of the marketers (in this case, spammers). The article goes on to mention that spammers use zombie computers to carry out their act, and infect these computers in turn. These infected computers could not only compromise the identity of the owner, but also serve as a content server through SOCKS proxying . Yet I have a lot of difficulty in digesting the claim "if you have an email address, there is a possibility that there is child pornography on your computer because you have received CP advertising. And if your computer is not 100% safe against Trojans, viruses and rootkits, there is the possibility that your computer is part of the vast child pornography network." I dont see how this would work with dynamic IPs. But then there are tools like DynDNS that take care of that?
If what the author says is to be believed, no doubt that so much effort goes into keeping an industry alive that would generate 200 mil site visits in a single month for a single website!
So how are these sites advertised? Apparently through spamming. The revenue from the child porn business are divided into 40-60% for the payment processor and the bank (percentage rate will depend on how hard the material is), 20% of the operator and 20% of the marketers (in this case, spammers). The article goes on to mention that spammers use zombie computers to carry out their act, and infect these computers in turn. These infected computers could not only compromise the identity of the owner, but also serve as a content server through SOCKS proxying . Yet I have a lot of difficulty in digesting the claim "if you have an email address, there is a possibility that there is child pornography on your computer because you have received CP advertising. And if your computer is not 100% safe against Trojans, viruses and rootkits, there is the possibility that your computer is part of the vast child pornography network." I dont see how this would work with dynamic IPs. But then there are tools like DynDNS that take care of that?
If what the author says is to be believed, no doubt that so much effort goes into keeping an industry alive that would generate 200 mil site visits in a single month for a single website!
Cryptic Treats
As part of our Human Factors in Security course, we were asked by our course instructor Cynthia, to start writing a journal, in which we put in our thoughts about security. It could include news articles, new ideas, thoughts on current trends, mental maps, anything that would put those grey cells to work. I haven't been able to find much time to do it though I really liked the idea a lot and enjoy the class every wednesday evening. It hadn't occurred to me till recently though, that i could write a blog instead of a really ugly word document! Hope this blog will have lots of content and be useful in the future :)
Subscribe to:
Comments (Atom)